-
Notifications
You must be signed in to change notification settings - Fork 0
/
Copy pathindex.html
392 lines (298 loc) · 11.1 KB
/
index.html
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
252
253
254
255
256
257
258
259
260
261
262
263
264
265
266
267
268
269
270
271
272
273
274
275
276
277
278
279
280
281
282
283
284
285
286
287
288
289
290
291
292
293
294
295
296
297
298
299
300
301
302
303
304
305
306
307
308
309
310
311
312
313
314
315
316
317
318
319
320
321
322
323
324
325
326
327
328
329
330
331
332
333
334
335
336
337
338
339
340
341
342
343
344
345
346
347
348
349
350
351
352
353
354
355
356
357
358
359
360
361
362
363
364
365
366
367
368
369
370
371
372
373
374
375
376
377
378
379
380
381
382
383
384
385
386
387
388
389
390
391
392
<!DOCTYPE html>
<html>
<head>
<title>Title</title>
<meta charset="utf-8">
<style>
@import url(https://fonts.googleapis.com/css?family=Droid+Serif);
@import url(https://fonts.googleapis.com/css?family=Yanone+Kaffeesatz);
@import url(https://fonts.googleapis.com/css?family=Ubuntu+Mono:400,700,400italic);
body {
font-family: 'Droid Serif';
}
h1, h2, h3 {
font-family: 'Yanone Kaffeesatz';
font-weight: 400;
margin-bottom: 0;
}
.remark-slide-content h1 { font-size: 3em; }
.remark-slide-content h2 { font-size: 2em; }
.remark-slide-content h3 { font-size: 1.6em; }
.footnote {
position: absolute;
bottom: 3em;
}
li p { line-height: 1.25em; }
.red { color: #fa0000; }
.large { font-size: 2em; }
a, a > code {
color: rgb(249, 38, 114);
text-decoration: none;
}
code {
background: #e7e8e2;
border-radius: 5px;
}
.remark-code, .remark-inline-code { font-family: 'Ubuntu Mono'; }
.remark-code-line-highlighted { background-color: #373832; }
.pull-left {
float: left;
width: 47%;
}
.pull-right {
float: right;
width: 47%;
}
.pull-right ~ p {
clear: both;
}
#slideshow .slide .content code {
font-size: 0.8em;
}
#slideshow .slide .content pre code {
font-size: 0.9em;
padding: 15px;
}
.inverse {
background: #272822;
color: #777872;
text-shadow: 0 0 20px #333;
}
.inverse h1, .inverse h2 {
color: #f3f3f3;
line-height: 0.8em;
}
/* Slide-specific styling */
#slide-inverse .footnote {
bottom: 12px;
left: 20px;
}
#slide-how .slides {
font-size: 0.9em;
position: absolute;
top: 151px;
right: 140px;
}
#slide-how .slides h3 {
margin-top: 0.2em;
}
#slide-how .slides .first, #slide-how .slides .second {
padding: 1px 20px;
height: 90px;
width: 120px;
-moz-box-shadow: 0 0 10px #777;
-webkit-box-shadow: 0 0 10px #777;
box-shadow: 0 0 10px #777;
}
#slide-how .slides .first {
background: #fff;
position: absolute;
top: 20%;
left: 20%;
z-index: 1;
}
#slide-how .slides .second {
position: relative;
background: #fff;
z-index: 0;
}
/* Two-column layout */
.left-column {
color: #777;
width: 20%;
height: 92%;
float: left;
}
.left-column h2:last-of-type, .left-column h3:last-child {
color: #000;
}
.right-column {
width: 75%;
float: right;
padding-top: 1em;
}
</style>
</head>
<body>
<textarea id="source">
class: center, middle
# Docker Know How
An Introduction to Containers
---
# Agenda
1. History
2. Containers
3. Linux Primitives
4. Docker
5. Docker breakdown
---
# History
- 2010: dotCloud YC funded
- March 2013: Solomon Hykes @PyCon 2013
- April 2013: Docker is released
- 2015: Open Container Initiative
---
# Containers
It is important to know that containers are not new this world, by any means.
- BSD Jails
- Sun Zones
- OpenVZ
- LXC - Still Active Development
Think of Containers as chroot on steroids, minus the virtualized hardware, and but with all the isolations primitives of a VM.

---
# Linux Primitives
Idea of containers is not new and they use three main kernel primitives, namespaces, cgroups and capabilities, to achieve isolation, control and privileges.
- Namespaces
- Cgroups
- Capabilities
---
# Namespaces
One of the overall goals of namespaces to support container isolation, providing the process(es) within them an illusion that they are the only processes in the system.
- Mount namespaces (`CLONE_NEWNS`)
- UTS namespaces (`CLONE_NEWUTS`)
- IPC namespaces (`CLONE_NEWIPC`)
- PID namespaces (`CLONE_NEWPID`)
- Network namespaces (`CLONE_NEWNET`)
- User namespaces (`CLONE_NEWUSER`)
---
# CGroups
CGroups provide a mechanisms to the derive quotas on the use of linux subsystems, and define mechanisms for processes to be restricted within these quotas.
- `cpuset` - assigns individual processor(s) and memory nodes to task(s) in a group;
- `cpu` - uses the scheduler to provide cgroup tasks access to the processor resources;
- `cpuacct` - generates reports about processor usage by a group;
- `io` - sets limit to read/write from/to block devices;
- `memory` - sets limit on memory usage by a task(s) from a group;
- `devices` - allows access to devices by a task(s) from a group;
- `freezer` - allows to suspend/resume for a task(s) from a group;
- `net_cls` - allows to mark network packets from task(s) from a group;
- `net_prio` - provides a way to dynamically set the priority of network traffic per network interface for a group;
- `perf_event` - provides access to perf events to a group;
- `hugetlb` - activates support for huge pages for a group;
- `pid` - sets limit to number of processes in a group.
---
# Linux Capabilities
At a very basic level privileges in linux come twos, `regular user` and `root`. If a regular user requires the do some privileges operation of say, using a port number lesser than 1024, the user might require root priveleges. Unfortunately giving root privileges to a user would be giving access to all the resources without limitations, and when that user gets compromized the options are unlimited. To overcome this linux came up with `capabilities` that give more granular restrictions on what a particular user could do on the system. Hence reducing the attack surface if that user is compromised.
---
# LXC
LXC provided good abrstactions over the Namespaces, CGroups and Capabilities, to contain linux images like ubuntu or fedora. This project is in active development, fixing many of the security and resource management flaws, as they try to me more mainstream. But somehow they failed to captivate the imagination as much as docker did. I feel that the reasons for these where
- It was positioned more as virtualization model than a packaging model
- Development was slow as it was a community owned project
- Barriers of entry was pretty, with much focus on the kernel primitives
- Interfaces were not conginitive enough for developer adoption
- Had not matured enough in the given time frame
- [Developed in C](https://github.com/lxc/lxc)
---
# lmctfy(lum-cut-ee-fy)
Seeing the emergence of docker, Google could no longer hide it's container ship behind the curtains of close source. In 2014, Google opensourced their container mechanism to work with a very strange name, lmctfy(Let Me Contain That For You). But failed to make any impact as the feature to feature comparison did not live up to docker's mechanics, also the [C++ codebase](https://github.com/google/lmctfy) meant it was for the elitists.
---
# Others in the Room
Well there were others([vagga](https://github.com/tailhook/vagga) and [rkt](https://github.com/rkt/rkt)) who challenged the monopoly that Docker was gonna be, but fell short. As much as I really want a true competition for Docker nothing really worthy has come around yet. In fact all that the challengers could do was the impact the course of docker, as you would see later in this writing.
---
# Docker
1. Docker is platform run containers.
2. docker is service that manages containers.
3. Docker is company driving the container movement. Docker Inc.
---
# Docker Evolution
---
# lxc
- [Docker as a facade over LXC](https://github.com/docker/engine/tree/5130d3d6ec979ea2d1f9a0da9d5766028571dd9e)
- LXC did the bulk of the heavy lifting
- Docker provided Image management
- docker was the the service and the client
---
# libcontainer
- [0.9.0](https://github.com/docker/libcontainer/tree/bfcd86f32d22096ae69a140a1fafc1bc42391b1c) release ships with libcontainer
- Interfaces with `namespaces`, `cgroups` and `capabilities`
- Provides interfaces to docker daemon
- Lead the way to become platform agnostic
---
# Monolith
Though docker was moving along pretty fast but there was one problem, the docker engine codebase it was still a monolith doing all the following operations.
- Providing docker API to the client to operate on
- Providing the image management services for creating and managing images
- Managing the container lifecycle by using `libcontainerd`
- Providing the network subsystem for containers to communicate with the host as well other containers
---
# Breaking the Monolith
- Ease of innovation
- Fast development model
- The ecosystem demanded the change
---
# OCI - Open Container Initiative
- [OCI](https://www.opencontainers.org/) uneder Linux Foundation
- [Container Runtime Specification](https://github.com/opencontainers/runtime-spec)
- [Image Specification](https://github.com/opencontainers/image-spec)
- `libcontainer` is donated to the OCI
- Docker Inc. contributes the specifications
---
# runc
- Reference is implementation of the OCI Runtime Spec
- Does only one thing, creates containers
- Wraps around `libcontainer`
- `runc` exits as soon as the container is created
---
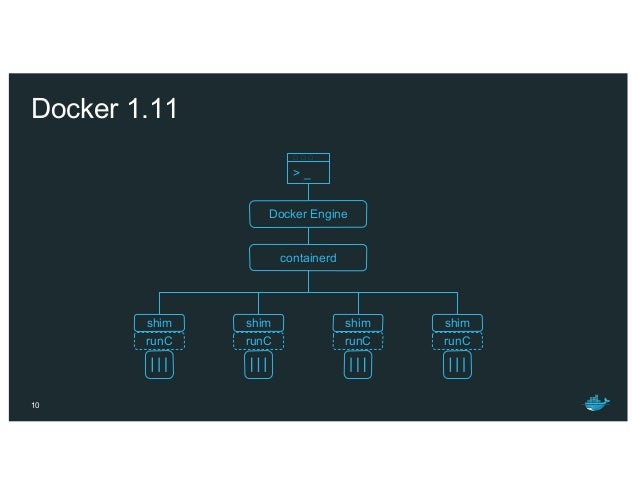
# docker-containerd
- Interface glue between the `dockerd` and `runc`
- Provides standard interfaces for container lifecycle managements
- Implements consumers for intefaces exported by OCI Runtime Spec
- Also includes image management
- Part of the [OCI](https://github.com/containerd/containerd)
---
# docker-containerd-shim
- daemonless containers
- Allows the runtimes to exit
- Owns up as parent of the running container
- Ensure the `dockerd` and `docker-containerd` could upgrade
- Reports back exit status of the running container to `docker-containerd`
---
# docerkd
- API interface to the docker client
- Implements interface with `docker-containerd`
- Provides network
- Provides storage
---
# Big Picture
The following depict all of the things we discussed above put together.
---
# Moby
- [Upsteam Opensource Project to Docker](https://github.com/moby/moby/pull/32691)
- Home for all docker componets
- Spun off in 2017
---
# daemon.json
- Docker starts with default configuration
- `/etc/docker/daemon.json`
- `man dockerd` to see defaults
- To debug set it in this file
```json
{
'debug': true
}
```
---
# Dockerfile
- Definition to build docker images
- Derives `FROM` other other docker images
- [Docker hub](https://hub.docker.com) is repo of images
- Verfied
- Non verified
- `RUN`, `CMD`, `ENTRYPOINT`
```
FROM alpine
RUN apk update
RUN apk add nginx
RUN mkdir -p /run/nginx
EXPOSE 80
CMD ["/usr/sbin/nginx","-g","daemon off;"]
```
</textarea>
<script src="https://remarkjs.com/downloads/remark-latest.min.js">
</script>
<script>
var slideshow = remark.create();
</script>
</body>
</html>